Veriato employee monitoring software provides unmatched visibility into the online and communications activity of employees and contractors.
Data
Purpose-built to collect full fidelity data on the activity of the people who interact with your IT resources and information.

Control
You control what data is collected and when. You control what you can access and review. Granular control provides the flexibility you need.

Visibility
DVR-like playback plus powerful alerts, intuitive search, quick view panels and scheduled reports minimize time spent getting accurate answers to support good decisions.


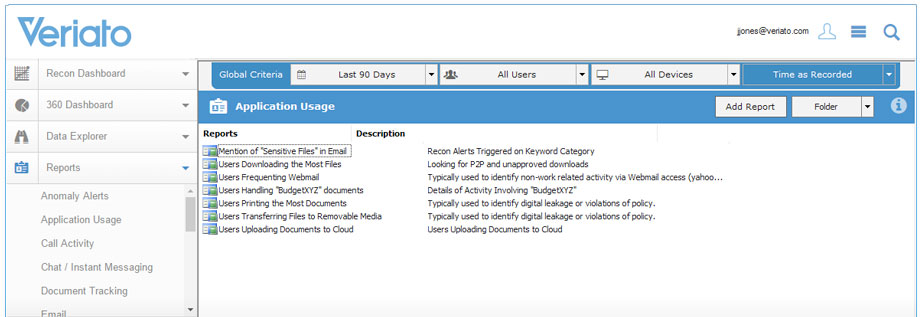
 Application Usage
Application Usage
 Document Tracking
Document Tracking
 File Transfers
File Transfers
 Network Activity
Network Activity
 Online Searches
Online Searches
 Websites Visited
Websites Visited
 Email / Webmail / Chat / IM
Email / Webmail / Chat / IM
 Login / Session Activity
Login / Session Activity
 Keystrokes
Keystrokes